No doubt Internet has dramatically changed the way people live and work. All this has been made possible by a set of different technologies. But nothing is perfect. Those technologies are not an exception. One of the core parts of the Internet is the Domain Name System. DNS does have certain issues but the respective organizations are working hard to continuously improve it.
Below we’ll explain what DNSCrypt is and how it helps users, and we’ll provide instructions how to set it up.
Domain Name System is a hierarchical distributed system that provides information about domain names. DNS work depends on a set of DNS servers that store information about domain names and the IP addresses assigned to their respective domain names. When a DNS server receives a request, it responds with the IP address for the requested domain.
DNS was created in 1983, then it was improved in 1987. The description of a system and its protocols could be found in the respective RFC documents: https://en.wikipedia.org/wiki/Domain_Name_System#Standards_documents
DNS has certain weak points and security issues because by design security wasn't the main concern. Since Internet became widely available to the general public, more and more issues were discovered. Those issues include DNS cache poisoning aka DNS spoofing. This type of attack provides spoofed data to the client from cached DNS information supplied by a malicious person.
The most known solution for this issue is DNSSEC. It that implements signed DNS queries and responses for the underlying protocol. This way DNSSEC ensures that all DNS queries are authentic and real and do not contain bogus data. In the meanwhile the DNS requests themselves aren’t hidden from anyone. Another problem is that DNSSEC is not fully implemented yet. While root DNS servers use this, not all ISP providers that have DNS servers support DNSSEC. This can be solved by using a specific public DNS server such as Google Public DNS or OpenDNS (now owned by Cisco).
The comprehensive way of improving DNS security is DNSCrypt. This is a protocol initially created by OpenDNS to provide encryption for the entire protocol and all communications between DNS client and server. It can be compared to SSL used with HTTP, i. e. HTTPS.
The project is actively developing on GitHub. It’s open source and anyone can contribute to it.
It is important to understand that full privacy on the Internet is next to impossible and can’t be achieved only by one specific technology such as DNSCrypt. This is because it won't hide your IP address or make you anonymous on the Internet. It just encrypts the DNS queries and will provide additional security – only if you use a trusted DNS server that supports DNSCrypt.
In most cases, the DNS server address is obtained via DHCP (with some variations in case of IPv6 or manual static setup). Then the host makes a DNS query to the servers and receives the required IP addresses and some other data (if needed).
DNSCrypt is a program which works as a daemon or service (and it also works as a proxy server). The program acts as an intermediary, receiving the queries, encrypting all the data and then forwarding it to the server. In many cases DNSCrypt works on localhost.
DNSCrypt is useful in the following cases:
The obvious advantage of DNSCrypt is data encryption. At the same time, it has some cons. The big one is that it is not standardized as an official extension of the DNS. This causes other issues such as availability for different platforms. While it’s available on the most widespread platforms, it requires manual installation on every device via third party software.
For example, for a regular user of an Android or iOS-based mobile device, it’s mostly impossible to install and use it. iOS is a tightly locked system and it won't allow any modifications. It’s sometimes possible to install DNSCrypt on a jailbroken device, but it’s often impossible with the latest available iOS versions. Android devices require root access and a modification in the system partition. On some devices, it’s not possible to install even with root access. Also, device rooting may (and often will) break warranty.
Installing DNSCrypt on desktop operating systems is easy as compared to mobile devices.
Because DNSCrypt is not an official standard, almost all routers with stock firmware from vendors have no support for it. Still, you can install it by either extending original firmware (if possible, and some vendors do allow it) or by installing custom additional packages for the firmware such as Tomato, DD-WRT, OpenWrt or AsusWRT-Merlin (which is a mod of the original firmware by Asus). Only Tomato (more specifically, some of its flavors) supports DNSCrypt out of the box. Others need package managers with Entware-ng repository (by the way, it provides a lot of additional software, not just DNSCrypt). Setup procedure for a specific device requires specific instructions per firmware and may vary.
1. Download the DNSCrypt binary package at https://github.com/jedisct1/dnscrypt-proxy/releases and unpack it (e.g. to C:/DNSCrypt)
2. Open elevated command prompt and go to the target directory:
cd C:/DNSCrypt
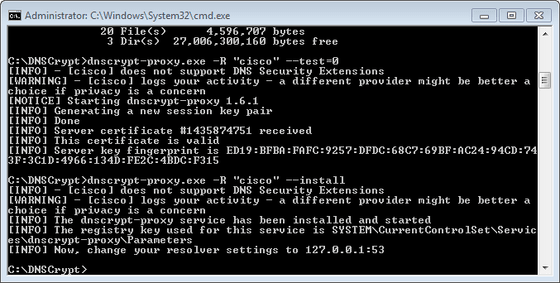
3. Run DNSCrypt (just for testing, no installation yet) with a chosen public DNS server. You can find the list of servers here: https://download.dnscrypt.info/resolvers-list/v2/public-resolvers.md The servers can be referred by their short names (see above link). Let’s try and use Cisco OpenDNS as an example:
dnscrypt-proxy.exe -R "cisco" --test=0
By the way, some DNS servers offer the additional benefit of filtering improper content (such as phishing and adult websites, etc.).
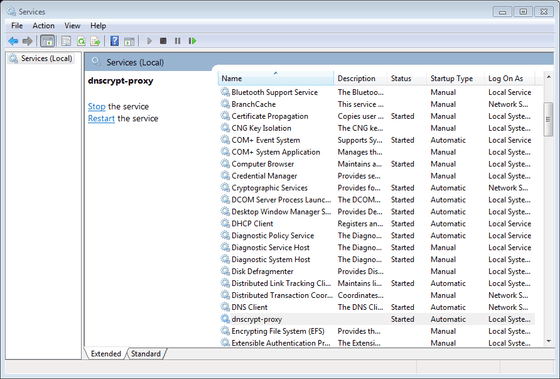
4. Run the following command to install DNSCrypt as a service:
dnscrypt-proxy.exe -R "cisco" --install
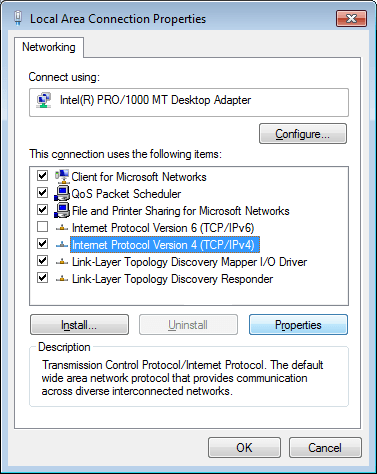
5. In your connection settings, change the DNS server IP to 127.0.0.1 so it will use the DNSCrypt proxy. In order to use DNSCrypt, do this for all network connections including wired and wireless networks (i.e., LAN adapters and WLAN adapters).
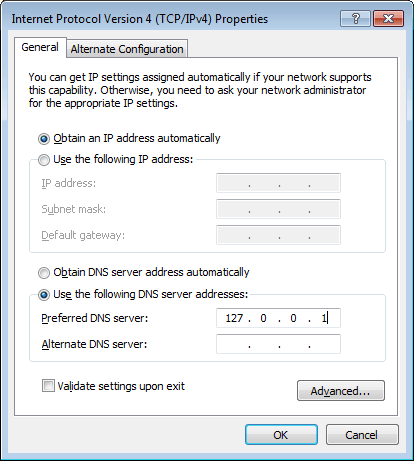
You can revert DNS to automatic DNS discovery using the same screen. Or, you can use the following command:
netsh interface ip set dns "Local Area Connection" dhcp
For easy DNSCrypt package management, Mac users can install a GUI-based program from https://github.com/alterstep/dnscrypt-osxclient
Alternatively, advanced users can use dnscrypt-proxy package from the Brew package manager:
$ brew install dnscrypt-proxy --with-plugins