We surely want all our private conversations to stay private. This is but simple and natural for any person. If we text or voice chat with someone, we want to be sure this space is personal and well-protected. Especially given that we occasionally send sensitive information that may be related to our family, health or business.
As of now, privacy is somewhat hard to achieve. Governments and companies may want to access our personal conversations. There are plenty of ways to send messages and most of them are insecure. Starting from pushing plain text over an insecure network, or (just a tiny bit more secure) rely on outdated or vulnerable protocols. There’s not much software out there that can provide real security for private messaging, and we’ll cover it in this review.
It’s important to understand that almost anything intended for tight security and relying on really strong tech can be hacked.
 |
Actually, the main problem often is the infamous human factor that’s vulnerable to social engineering. Even if you use the most secure protocols and latest software updates, it won't help if your password is a variation of 12345 and you wrote it under your table (or on a paper in your wallet).
The second concern is that such services are provided by third parties, and you must understand that trust is a big issue here. Meaning that such a provider can be compromised and your data can be stolen and even worse – the provider might sell the data elsewhere.
The third concern is a wide range of software that takes part in the whole workflow (including the network stack). Some parts can be broken, others may contain issues and so on. There's no guarantee that the security is tight throughout the entire chain.
It is important to understand that even secure chat messengers cannot guarantee protection at all levels. The only function of those protocols and software is to transfer and encrypt messages (plus, audio and video calls). All of the above has been designed and implemented by hundreds of different authors and nobody can guarantee it’s free of vulnerabilities or even intended backdoors. The software works inside an operating system which is also potentially vulnerable.
Actually, you can’t be absolutely safe even if you unplug the network cable (see the ‘social engineering’ concern above).
To sum it up, even the best message encryption isn’t of much use if other aspects of security aren’t taken care of. If you think that someone’s after your data, then the best thing you can do is avoid sending critical data by electronic means (and tell about the concerns to the police).
The OTR protocol is a general-use protocol that can be used almost in any IM chat if appropriate software available for your IM platform. OTR was created in 2004 and it provides end-to-end security for instant messaging chats. It can be used via XMPP (aka Jabber) or any other chat system. In this case IM is a means of data transport and OTR is responsible for:
Why it is important to use OTR? Google Hangouts, Facebook Messenger or XMPP transfer data over a secure channel (i.e. HTTPS) but it doesn't hide those messages from the servers and companies (i.e. Google, Facebook and XMPP provider). With OTR, messages are encrypted and cannot be accessed by a third party. Only conversation members can read it.
OTR only works when both sides use the protocol. If your talk partner doesn’t use it, then there's still a way to talk over a protocol without OTR. But then it won't be encrypted. The latest versions of the protocol (version 3 since the 4.0.0 release of libotr) provide a way to talk to your buddy who logs in from different locations (i.e. from different devices).
One more way of using OTR is install Pidgin (a multi-protocol messenger) and the OTR plugin for it. During the setup, ensure that authentication is obligatory at both ends. If so, it will indicate that the conversation is private. A comprehensive instruction for Pidgin and OTR for Windows is available at https://ssd.eff.org/en/module/how-use-otr-windows If you want to use a different chat client over OTR, refer to the official documentation for your chat client.
While almost all message services are dependent on provider’s infrastructure and close-sourced, XMPP is an open source project. It is possible for everyone to install their own server and use messaging with full control and full encryption.
Project page: https://telegram.org/
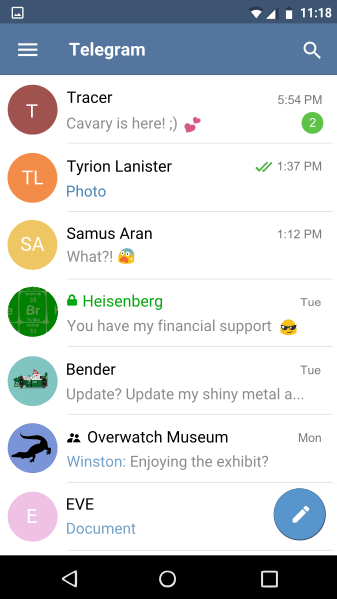
Telegram was founded by an exiled Russian entrepreneur and the founder of the biggest Russian social network Vkontakte Pavel Durov (as an investor) an his brother Nikolay Durov (as a developer). Telegram has quickly gained momentum over the last year. While its most functions are typical for any IM, the most interesting feature is secret chat providing strong security.
Telegram is based on the protocol called MTProto. It relies on a central server so the whole architecture is based around it. General use chats are not secret, so it makes little sense to use Telegram for those chats. Telegram doesn't provide audio and video calls, and group chat doesn’t have strong security.
Telegram clients are available for a wide range of operating systems including Android, iOS, Windows, OS X, Linux and many more (for a full list of a supported platforms, see the official website). All clients are open source and the code available on GitHub.
While there are a plenty of platforms where Telegram is available, secret chats do not support all of them. Supported ones include Android and iOS. Also, Pidgin also provides support for Telegram’s secret chats via an unofficial plugin.
Secret chats are meant to encrypt messages between two sides of conversations only, and as such they are not supported for group chats. Also, it is impossible to synchronize messages and use the same conversation on different devices. That is because a secret key is required to use the chat and it’s stored on the device and can’t be transferred.
Project page: https://whispersystems.org
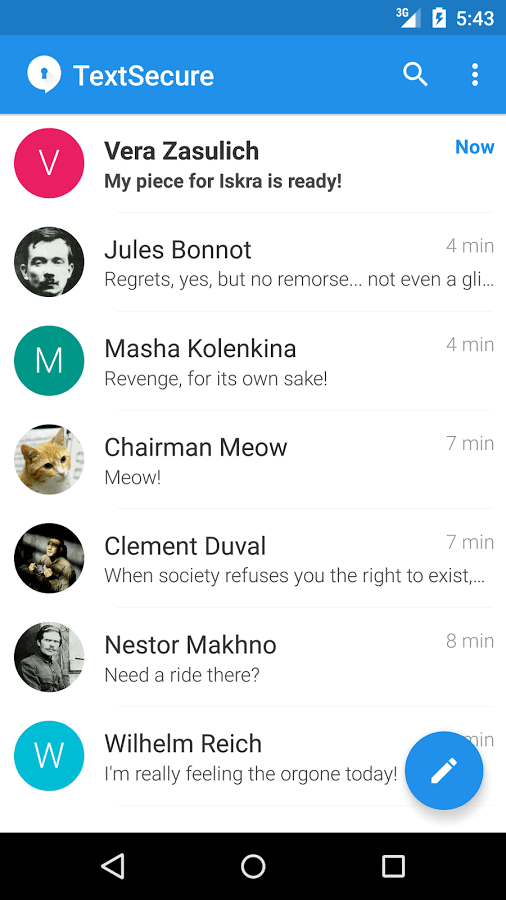
Signal was developed as two products: TextSecure for text messaging and RedPhone for audio and video calls (both secure) by Whisper Systems. This was a private company which was later acquired by Twitter. Later, RedPhone became unavailable while TextSecure was still working. The original authors Moxie Marlispike and Stuart Anderson founded a new non-profit company Open Whisper Systems which is responsible for the development of Signal nowadays. TextSecure and RedPhone were merged into one single project Signal.
Signal is another messenger with end-to-end encryption. The difference from Telegram is that it provides encryption for all chats by default, so there's no way to read the messages on the server side. However, end-to-end encryption implemented this way makes conversations possible only between two specific devices. There's no way to synchronize messages between multiple devices. Still, you can use the desktop client, but it only supports linking with an Android device and can't be used without it.
Signal uses the TextSecure protocol which is based on the Off-the-Record protocol. The project is open source and available on GitHub. Another huge advantage of Signal is support for encrypted audio and video calls. To this end, it uses the RedPhone protocol which is based on the ZRTP & SRTP protocols.
Signal requires a phone number for registration and works only on smartphones. The disadvantage of this application is that it’s only available from official stores such as Google Play and App Store. While there're no alternative channels for distributing apps for iOS devices, Android users can install software from unofficial sources. Authors of the application do not encourage distributing application from sources other than Google Play.
Another problem is that Signal requires Google Play Services to be installed. Recent statements say that Signal does not rely on Google Cloud Messaging (a system for delivering push notifications) and uses its own infrastructure. Still, it requires Google Cloud Messaging for waking phone in order to receive new messages properly.
Project page: https://tox.chat/
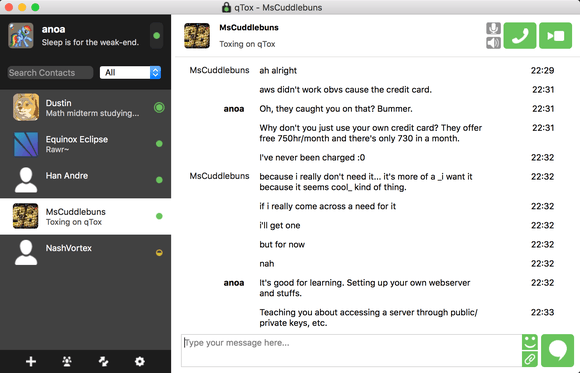
Tox is another project intended to provide secure transport for conversation over the Internet. Tox supports text messages, audio & video calls.
The project is still under active development and there's no officially stable version at this time (however, it is actually stable and ready to use and works without major issues). The main advantage of this software is that it is decentralized and isn’t locked up on a single company. The problem with many other services is that most of them are provided by one company. Some of them can read all users messages, others just rely on a company's infrastructure and there's always a possibility for it to be compromised.
Tox doesn't require any registration or even a phone number (unlike Telegram or Signal). In regards to its model, Tox is similar to BitTorrent because it’s a peer-to-peer protocol.
Tox is available for a wide range of operating systems including Android, iOS, Windows, Linux, OS X and so on. The entire feature set is not implemented across all the clients. The most feature rich are uTox and Isotoxin. The full list with a description and comparison can be found here: https://wiki.tox.chat/clients.